So, count me as #2 out of those thousand people who have read his column, and actually agree with it. The problem is that we need the majority to wake up from their consumer era dream, and get back to work, making adult decisions, for our own sake, and our children."The motoring era is coming to an end. Heroic investments in highway infrastructure to create jobs will be a tragic waste of our dwindling capital. The pressure for Mr. O to make these misinvestments will be enormous, perhaps insurmountable. There are probably not a thousand people in the US who agree with what I am saying -- meaning the consensus to keep the cars running at all costs overwhelms reality at the moment. Does Mr. O's concept of "change" include the possibility that we may have to live very differently in this society?Chances are, if Mr. O knows any of these things he might be crucified in the polls and the media by acknowledging them. The only "change" that America really wants to hear about is evicting George Bush from the White House."
Tuesday, December 02, 2008
Count me as #2 of 1000
Saturday, November 29, 2008
Acer Aspire One - 20 days later
- It's small
- It has no optical drive
Friday, November 28, 2008
Hard Target Search - Neologism
He stops and looks into the TV lights and starts moving downtrack. The media and State Police move with him like Israelites behind Moses.
GERARDLadies and gentlemen... our fugitive's been on the run for ninety minutes. Average foot speed over uneven ground - barring injury is approximately four miles an hour, giving us a radius of six miles. I want a hard-target search of any residence, gas station, farmhouse, henhouse, doghouse and outhouse in that area. Check-points go up at 15 miles.(to media)You got that? Good. Now, turn those damn things off and get out of our way.
- any fortified, reinforced, armored, or protected object, mobile or stationary, which may require special ammunition or specific tactics (eg: sequence, approach, etc), and serves as a FORCE MULTIPLIER when attacked; see HARDEN, OBJ, COLLATERAL DAMAGE, RULES OF ENGAGEMENT (ROE), RFZ, NFZ, FREE FIRE ZONE, BDA, IRONCLAD, SKIN; compare SOFT TARGET.
ELAINE: Well, Kramer was right. My friend Kim told me the sponge is off the market.JERRY: So what are you gonna do?ELAINE: I'll tell you what I'm gonna do - I'm gonna do a hard-target search. Of every drug store, general store, health store and grocery store in a 25-block radius.
Friday, November 21, 2008
Poor mans geofiltering - The Zip Code
Wednesday, November 12, 2008
Tiny bubbles - and why you should care a bit
The photo on the screen is available from my Flickr photostream.
I couldn't resist playing with it in an almost recursive fashion... so I ended up with this:

So now I'm 45. I'm still amazed I lived past 28, and grateful for every day.
Tuesday, November 11, 2008
Change.gov - post 3
Social network networks
Monday, November 10, 2008
Recieved wisdom - saving for later
Change.gov - post #2
To do this, we should encourage Internet access for all Americans. One very low cost way is to help encourage a culture that shares this resource. The recent FCC rulings concerning "White Space" or unused radio channels are a great step forward. We should also encourage the FCC and others to allow communities that wish to build their own Internet infrastructure, instead of forcing them to wait for one of the incumbent monopoly providers to decide it's worthwhile.
The Internet was meant to be shared, anything you can do to help would be greatly appreciated.
Sunday, November 09, 2008
New tools
Friday, November 07, 2008
Songs about teamwork
Thursday, November 06, 2008
Change.gov is now online, and accepting suggestions
Create an commission responsible for auditing and reviewing every branch of government, composed of at least 50% certified public accountants, and the balance from the general population. Set it up so that it would be treated like Jury duty.... it would be a public service, and NOT a permanent position. Like Juries, they would pick their own foreman once they were qualified and grouped and given a section to work on.
I've got a few more to type in.
Monday, October 20, 2008
Chicago Bean Panorama - Prints Available
Thursday, October 16, 2008
Old posts - adding value to the archives
Why I blog, and what to do afterwards.
This form of instant and global self-publishing, made possible by technology widely available only for the past decade or so, allows for no retroactive editing (apart from fixing minor typos or small glitches) and removes from the act of writing any considered or lengthy review. It is the spontaneous expression of instant thought—impermanent beyond even the ephemera of daily journalism. It is accountable in immediate and unavoidable ways to readers and other bloggers, and linked via hypertext to continuously multiplying references and sources. Unlike any single piece of print journalism, its borders are extremely porous and its truth inherently transitory. The consequences of this for the act of writing are still sinking in.
Blogging tools still suck
Monday, October 06, 2008
The Bailout and how we got there... actually explained.
Thursday, October 02, 2008
Quote of the day
Wednesday, October 01, 2008
Bailing out the world?
Learn from History
The Smoot-Hawley Tariff Act (sometimes known as the Hawley-Smoot Tariff Act)[1] was an act signed into law on June 17, 1930, that raised U.S. tariffs on over 20,000 imported goods to record levels. In the United States 1,028 economists signed a petition against this legislation, and after it was passed, many countries retaliated with their own increased tariffs on U.S. goods, and American exports and imports plunged by more than half. In the opinion of most economists, the Smoot-Hawley act was partially responsible for the severity of the Great Depression.[2][3]
Here we go again.... damn thieves are trying to rip us off again!
Tuesday, September 30, 2008
My Congressman Rocks!
Dear Michael:Thank you for contacting me to express your concerns regarding government assistance to distressed financial institutions.I absolutely agree with you. That is why today I opposed H.R. 3997, the Emergency Economic Stabilization Act of 2008, and the House rejected it by a vote of 205 to 228.I do not believe that it is the responsibility of Congress to bail out financial firms experiencing loss because of a lack of regulation, a lack of oversight, the greed of financial executives who often make sums in excess of 250 times the income of the average American worker, and bad judgment.I have the gravest reservations over this proposal, and I am appalled at the President's arrogance to suggest that Congress act within ten days to undo a disaster that has crescendoed over the last ten years and enriched countless Wall Street executives and speculators while impoverishing multitudes. Enclosed, please find a copy of the remarks that I submitted for the Congressional Record during consideration of H.R. 3997.The problems in our current financial system are not temporary aberrations in an otherwise healthy system, and may not be so easily addressed. As I write, it is not known whether similar proposals will be considered in the future. However, given the gravity and systematic nature of these problems, you can be assured that I will examine any future proposal with the same care and deliberation I exercised with H.R. 3997.Thank you again for contacting me. Do not hesitate to let me know if you have any other questions or concerns.Sincerely,Peter J. ViscloskyMember of Congress
Monday, September 29, 2008
The people have spoken... for now...
What the bailout really means
Bad word of the day - Webinar
Sunday, September 28, 2008
My plan to resolve the mortgage crisis... ugly, but effective
I believe that mortgages are a symptom, and not the real problem. Trust and transparency allow us to have expections that actually get met. Nobody knows what Paulson will do... which is going to make things worse, regardless of his actions.
Cluetrain urgently needed
Saturday, September 27, 2008
The clearest explaination of the bailout, ever!
Thursday, September 25, 2008
Sneakernet 2.0
Never underestimate the bandwidth of a station wagon full of tapes hurtling down the highway. —Tanenbaum, Andrew S. (1996). Computer Networks. New Jersey: Prentice-Hall, 83. ISBN 0-13-349945-6.
Sunday, September 21, 2008
Pissing in the wind
They made bad loans, they deserve to pay for it, not me and my child.
DON'T BAIL OUT WALL STREET
Saturday, September 20, 2008
More information needed in hyperlinks
- agree
- disagree
- have an update
- think it's funny
- want to tag an entry
- add a comment
Rebuilding the 4th estate
We need Social Journalism... NOW
- RICO - claim it was drug money, force the rightful owner to PROVE it wasn't
- Terror - claim they were supporting terrorists, throw them in jail
- Retirement - allow the holding firm to raid your pension
- US Dollars - fudge the inflation numbers and print as much as you want to spend
- Stocks - the DOW isn't keeping up with inflation
- Houses, Land - Emminent Domain
Thursday, September 11, 2008
Post 9/11 photography on the CTA - Entirely Reasonable
Wednesday, August 27, 2008
NSclient++ Error 2755 - Solved
Real Change - End the empire, restore the Republic
If we settle down, get our own house in order, and play nicer, we might just survive another 200+ years, otherwise we're in for a chaotic inevitable decay.
This is the first in a series of blog posts to flesh out the list from yesterday.
Monday, August 25, 2008
What do you think REAL CHANGE means?
Now we see the true colors of Mr Obama starting to come out. He has chosen a running mate who has none of my views, and doesn't represent anything other than the status quo.
Our country is broken, and facing extinction, and all we get is more bread and circus... the shit storm is coming, and it won't be pretty. I don't think Obama represents enough change, and it's discouraging. I let this sit while I thought about it overnight... this morning a new twist arrived, in a comment on his blog, Doc Searls asked
what would real CHANGE be?
This gives me an opportunity to turn this around into a positive, and I'm glad.
Here's my list, off the top of my head:
- Admission that we've been covertly building an Empire, and a promise to stop, and support Democracy around the world instead.
- Admission that we're hooked on foreign fuels, and we need to break this addiction, starting now. Immediate tariffs on imported fossil fuels to start paying off the national debt.
- Admission that we've been bought and paid for by lobbyists from all over the world, and it will stop now. Lobbying undermines the Constitution, and thus is a form of Treason.
- Admission that the shift from the Gold standard was a mistake, and an immediate return to the Gold standard at $2000 = 1 Ounce, giving everyone a one time 50% inflation hit, instead of the 5-10 years of 17% inflation like the 1970s. After that, no more inflation, ever.
- Trials for High Crimes and Misdemeanors of those involved in the planning and promotion of the Iraq war, which caused the death of over 4000 Troops, countless other injuries both physical and mental, along with well in excess of 100,000 civilians, and hundreds of thousands of displaced persons. Not to mention the trillions of dollars lost.
- Immediate dissolution of both Fannie Mae and Freddy Mac, with the bondholders receiving whatever is left after costs are recovered by the US Government. Shareholders would get nothing.
- Elimination of the Electoral college, replaced with a 1st/2nd/3rd choice system of direct election of the President. The VP would serve at the discretion of the President, subject to Senate confirmation.
- Phased withdrawal of US troops from all foreign bases, including Gitmo.
- Allocating at least 1/2 of all radio frequencies for use of the public to allow a free national wireless internet.
Hows that for a start?
Tuesday, August 19, 2008
Running from the Coyote
I've decided to see who else is writing about the same thing.
It seems to be a lot smaller this year.
Friday, August 08, 2008
How do you mark your enemies in social networks?
Thomas Hawk (not his real name) is a "friend" of mine. I like his photography, and he seems to be very positive in supporting others. Like me, he's a fan of photographing the world around us, including art.
- Keep your friends close, and your enemies closer.
- Sun-tzu
Chinese general & military strategist (~400 BC)

The Broken Pitcher - William Adolphe Bougereau
Recently, MoMA, the Museum of Modern Art in San Francisco decided to change its policy to allow non-flash photography in the galleries, he signed right up.
Simon Blint is an asshole. He decided that the new policy doesn't allow for non-flash photography if you have a dSLR. This lead to him forcibly ejecting my friend from the museum.
This leads me to a new conundrum... how do I tag someone as my newest enemy in all of my social networks? Facebook doesn't have a way for me to tag him as an ENEMY, which is a very odd exclusion if you think about it.
Hating someone, or something, is one of the primal urges to action that gets a lot of things done in the world. Social networking should include a way to DEMOTE someone like this twit, or cops on power trips, or whatever. Social networks must allow for this basic and essential expression of anti-value if they are to truely be useful.
I believe that we need to add enemy lists, twit lists, etc... into the framework of VRM as well. This can only help us to label spammers, scammers, and other undesirables quickly and efficiently.
A social network that doesn't allow you to include your enemies isn't worth having.
The Vista Dead Pool
I won't miss it, unlike OS/2.
Monday, August 04, 2008
My elevator pitch for BitGrid
I've got a blog up at http://bitgrid.blogspot.com where I write about this subject, trying to get a chip made some day.
The idea is simple, really... a grid of cells with 4 inputs, a look up table, and 4 outputs. The 64 bits determine the outputs for any possible input combination.
Routing logic is even simpler... there is none. If you want to route through a cell, you have to program the cell to do it.
Thus any cell can be routing or computation, or both.
An unsigned n bit adder takes n cells
An unsigned n bit multiply takes n*(n-1) cells
A divider takes (n+1)*n cells, unless you want to divide by zero...then it's (n+1)^2 cells
Sound interesting? Waste of time?
I'd like to know what you think.
Friday, August 01, 2008
Blogging at the end of the long tail
Doc Searls is one of the bloggers I read on a daily basis. He's consistently promoted blogging as a way for us to express ourselves and help each other out. I recently posted comments about the nature of blogging out here in what's known as the "long tail"... so described because if you graph the amount of readers of traffic amongst all blogs, I'd be out in the long tail with most other blogs, having only a few readers.
Here's the basic dynamic, based on an illustration I grabbed from WikiPedia:

The environment that Doc is used to is radically different than the one the rest of us live in. Because he's got a stream of followers, he gets constant feedback on how he's doing. Out here in the tail, comments are a rare occurrence. The torrent of attention becomes a trickle out here. Thus the dynamics that work for him don't play out in the long tail.
It's more likely that someone will leave a comment for Doc, because more people read his work. It's also true that the person leaving the comment is more likely to get other people to read their comment as well, because comments are usually public. Private comments like emails don't enter this picture, but I strongly suspect they have correlation with popularity as well.
The positive feedback loop that helps push up the top bloggers works for the other end as well, the top get pushed higher, and the bottom gets pushed lower. Someone on the long tail might have a few interested followers, but they will likely not bother to go through the hassle of signing up to put a single comment on a web site. An email, or offline comment is the more likely route.
Then there is the male culture factor...
As men, a blogger starts with a disadvantage. Guys like to solve problems, we’re taught not to comment on things unless we can solve a problem, or have our 2 cents to throw in to a discussion. This is why we make crappy bloggers, we’re not good at the blog relationship thing, because we don't give lots of feedback.
We’re also impatient… it takes YEARS to find an audience, we’re used to getting new skills by working hard, the harder we work, the faster we get better…. blogging isn’t like that.
When you’ve got no traffic, it also doesn’t make sense to put things in separate blogs… so the audience you do have gets a lot of stuff they don’t care about… which discourages them as well. In my own case I’ve realized this and am in the process of separating out my areas of interest into different blogs. Most of them get NO hits on a given day… and one or two every once in a while thanks to random web searches. Is it really worth it?
Summary...
Do we have a voice in this bold new world or not? From out here on the long tail, it’s VERY hard to tell.
I think the #1 thing we can all do is to make it a point to at least leave 1 comment per day on someone’s person blog. Like complements, they only have value if they say something positive, and are true.
In other words, The love we share, is the love we receive.
Monday, July 28, 2008
The Quest for the Ball?
Thursday, July 24, 2008
Wednesday, July 23, 2008
The future is Usenet, all over again
- Anonymous posting will be prohibited
- Tags will replace the hierarchy of groups
- Digital Signatures will prevent forgery
- All posts will have URIs so we can still link to them.
- We still won't be able to markup hypertext. (a pet peeve)
- Data will be streamed instead of batch mode.
There were a lot of things to like about Usenet
- Push model saved bandwidth
- Aggregation was built in
- Group hierarchies helped increase signal to noise
- It was federated from the start
- Binary attachments were supported
Tuesday, July 15, 2008
DNS -- It's worse than I thought - Technical version
As most of you know, DNS (Domain Name Service) is the system by which names such as www.apcu.org get translated into numbers that the computer can use to connect to systems on the internet.
There is a very deep and serious flaw in design of DNS which affects virtually everyone, which was recently discovered. The technical details of this flaw are still being kept secret, but it has been disclosed that part of it involves the nature of requests from DNS clients when they do a "recursive" lookup. Here's a link that explains the details: http://www.inetdaemon.com/tutorials/internet/dns/recursive.shtml
It appears that if you know what someone is asking for, you can answer their next question, even if you're not supposed to. This means that you can't trust the answers from your DNS if it happens to be one of the vulnerable ones. (The ones that haven't been patched yet)
The situation is complicated, and made worse by the NAT (Network Address Translation) that we all use to share an internet connection among more than one computer. All of those Linksys, Belkin, Dlink, etc… devices we bought make it easier to guess the next question… if your DNS is behind one of them. This means that anyone with a Windows Domain, or Linux Server who has their own DNS now has to consider moving the DNS back outside the NAT… which isn't a nice prospect.
The DNS clients built into ALL of our PCs need to be updated as well. This means doing Windows Updates for ALL of your PCs
Fortunately, there is a tool to help you test your system (not just your DNS, but the whole chain) to see how you will fare (it's not a guarantee, but a guideline) available online at:
It's on the right side of the screen… conviniently labeled "Check My DNS".
It turns out I'm ok at home because ComCast has patched the servers I use… but I've got a ton of work to do at work.
There will be full public disclosure of the vulnerablity on August 6, 2008. I strongly urge you to use this time to get ALL of your systems tested and patched appropriately before the hackers of the world learn the details.
I'll be spending a lot of time on this… and so will most of you, it's far better to do it now than to have to clean up a mess afterwards. (When you can't trust your DNS to get the patches, etc!)
Monday, June 23, 2008
Exim is a bit nuts
All attempts to send email to myself resulted in replies which contained the error:
all relevant MX records point to non-existent hostsThanks to this entry on the PkgExim4UserFAQ, I was able to get a clue
A probable cause for this might be that all MX records for the offending domain point to site local or link local IP addresses, which are ignored by the dnslookup router to protect from misconfigured external domains. The default configuration has relaxed checking for domains that the local system is configured to allow relaying to, so adding the offending domain to dc_relay_domains will most probably help. Please note that this entry might be necessary anyway to bypass relay control for the domains in question.Well, I did the requisite test, to find this among the outputPlease note that no domain on the public Internet should have MX records pointing to site local or link local IP addresses, so you might check your externally visible MX records.
If this doesn't help, try analyzing the output of exim -d -bt some.local.part@the.offending.domain.example
ignored host mail.xxxx.com [10.0.0.x]
Ignored host?? Clearly not the same as one that is non-existent. So... the first error was a lie.
All the relevant records pointed correctly to a very much alive and well host, but exim chose to ignore it because it was local.
In order to get around this, you have to follow the suggestion of Marc Haber and tell it that it is going to relay email for your local domain (which sounds like a very bad idea) in order to get it to work.
I don't know why they did it this way, but I'm posting this here to help others figure it out.
Monday, June 16, 2008
XP era ends?
XP era ends: Will Vista step up?
Larry assumes that Vista is inevitable, and that anyone who questions it is unpatriotic... er... just a complainer. He then goes on to the straw men:
Now, the false choice here asserts that all non-Vista operating systems will suddenly and completely have no value once Microsoft, in their infinite wisdom says so.If you’re a Vista complainer you have two options from here:
- Move away from Windows completely (users try a new OS and developers jump ship).
- Or shut up and go with Vista.
There are a lot of reasons to avoid Vista like the plague. People went along with having pre-loaded Windows back when new versions were generally an UP-grade... but Vista breaks far too many things, and causes way too much grief. There is a lot of user hostility being build up over this, causing people to start searching for alternative platforms as an escape route.
Linux seems to be the platform of choice, be it on a Mac or a PC. We can all run XP under VMware if we need to run some application that can't get ported eventually to Linux. Microsoft is quite aware of the place they are putting everyone into, but really has no choice in the matter. They desperately want to keep their OS market share to help drive their Office cash cow, but know that this is ultimately a losing proposition. So they will keep the drama going, probably announcing some form of "extended support" to keep it alive for a while longer to prevent defection to Linux.
The XP era is ending, long live Linux.
Sunday, June 08, 2008
166437 and counting
Friday, June 06, 2008
Mellon Collie
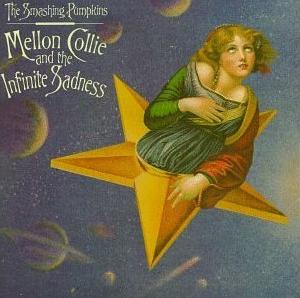
I got a nice spiffy new hard drive to gather all my photos together on... only to find out that I may have lost a few years worth due to inadequate backups... ugh, I'm feeling a bit of Melancholia.
My main task now is to fight through this, and try to recover what I can. Ugh!
Update: I have all of them in a lower resolution format... good enough for small prints... still working on getting the originals back.
Tuesday, June 03, 2008
Towards a new database model
The current crop of SQL type databases are all batch oriented. They just don't scale well because of this. We need to update the model from one of data that gets visited by the occasional query to one where the queries are always running and updating their results.
If you find yourself requerying a database without having changed the data yourself, you're wasting a huge amount of resources. You really only want to know what's changed, and it's silly to re-examine everything that isn't modified since the last run of the query.
Imagine a table in a database. If you recorded the initial state of the table, and all of the subsequent operations, you could perfectly replicate the state of the table.
If you then wrote code to implement this type of logic, it takes a lot less code to keep valid replicas. You would have a stream of changes instead of a set of facts that constantly needed to be reexamined.
If you ran a query against such a table, then ran the query against the stream of changes, you could have a running output that worked vastly more efficiently, since you only have to examine records that have changed.
I'm not a computer scientist, nor an engineer, but it seems to me that this model should be looked into a bit, and has some promise to save us all some time and effort.
Who knows, it might even save Twitter.
Saturday, May 31, 2008
Dead D40... ugh!
The shutter is fubar... when you turn it on it says
! Error: Press shutter
release button again.
Oh well... time to dig out the Coolpix 8800 and get the batteries charged.
Friday, May 30, 2008
Flow based databases to fix twitter?
I believe that this is a perfect case for a new type of database, and perhaps even a completely new framework of programming. I don't have a good name for it, and the ideas are still vague in my head right now, but I'll try to outline what I'm thinking of below.
I would break Twitter up into a series of tables which get distributed and replicated among a cluster of servers. The tables would relate to each other, but not in the strict atomic transaction model, but one of eventual consistency. These tables would be:
- Users
- Queues
- Subscriptions
- Content
The bandwidth external to Twitter is pretty high, because you've got lots of people with many subscribers. The amount of actual non-duplicate data is surprisingly small... and I'm guessing that it's on the order of 3kbytes/second. The real challenge is distributing this 3kbytes in a consistent and reliable manner to all the places it gets copied out.
A flow based database would be able to handle such types of loads by maintaining many local copies and keeping them in eventual consistency by tying them into a channel. This is a place where multicast might be a really good strategy, if not a straight peer-to-peer network.
A flow database could be a straight up normal table in an RDBMS, or it could be something new optimized to the task.
What do you folks think?
Oh my G-d, Scoble killed Twitter...
As if...
As I've stated before, the aggregate flow of all tweets in on the order of 10-20 messages per second, based on peeking at the message sequence numbers. It seems readily apparent that they've chosen the wrong architecture for this.
The tweets themselves should be aggregated with a sequence number, and user sequence number into a stream which should get copied to all of the boxes handling User Interface. Deleting a message would be handled by reposting it to the same queue with no data.
The subscription lists should be another stream.
The user database could be yet another stream.
All of those streams should aggregate out to about 10 kbytes/second. The process of splitting out the work to UI boxes is one of straight forward partitioning of the load, and maintaining a list of tweet sequence numbers for each person to see. The aggregated total of all of the three streams would sit on each UI box so they didn't have to get any of it from across the net.
That's my basic idea for scaling twitter. Comments welcome.
Sunday, May 25, 2008
Tim, Noran, Virginia, Bear
 Here's a great photo of Tim, Noran, Virginia and Bear. We took Virginia to the Lincoln Park Zoo in Chicago to celebrate her second birthday. Tim was nice enough to meet us there for the occasion. A fun day was had by all.
Here's a great photo of Tim, Noran, Virginia and Bear. We took Virginia to the Lincoln Park Zoo in Chicago to celebrate her second birthday. Tim was nice enough to meet us there for the occasion. A fun day was had by all.Bear got to see some of his cousins.
Greta still remains missing. She was last seen near Niagara falls a few years ago.
Thursday, May 22, 2008
Rememberance
 In Flanders fields the poppies blow
In Flanders fields the poppies blowBetween the crosses, row on row,
That mark our place; and in the sky
The larks, still bravely singing, fly
Scarce heard amid the guns below.
We are the dead. Short days ago
We lived, felt dawn, saw sunset glow,
Loved, and were loved, and now we lie
In Flanders fields.
Take up our quarrel with the foe:
To you from failing hands we throw
The torch; be yours to hold it high.
If ye break faith with us who die
We shall not sleep, though poppies grow
In Flanders fields.
— John McCrae
This is a day to remember those who came before us, and to reflect upon the legacy they left for us.
The time is now, always now, to decide what you can do to make the world a better legacy for our children.
Tuesday, May 20, 2008
Hezbollah has fiber?
Sunday, May 18, 2008
ACL as punishment?
Chris Saad injected the data portability meme into the flow and suggested personal Access Control Lists, in the form of a “Sharing OK/Not OK” check box on data you give to individuals or companies. It would be interesting to watch Robert Scoble manually configure a complex ACL on his 20,000+ friends (Scoble rushes in where Angels fear to tread).
While it would truly be torture to force a person to manually configure an ACL for 20,000 people, it doesn't have to be that way. One wrong move, and you've lunched everything.
Giving away capabilities on the other hand would be a much easier thing. You have the host environment generate a capabilities token for the piece you wish to delegate access to, then send it through email, or on a web page, or whatever the end user's security policy specifies is the right thing to do.
It would make far more sense to have a system that lets users delegate capabilities to any given part of their information, blog posts, photos, etc. The fact that you start with a model of least privilege means that you start with the most you're willing to give away, and pare down from there. You don't have to worry about giving away the store by mistake.
Yes, Access Control Lists would be punishment, but being able to give away little bits, without fear, is a quite liberating alternative.
I look forward to the future.
Saturday, May 17, 2008
QWERTY Considered harmful?
Larry Wall’s first rule of computer language design is, “Everybody wants the colon”3. Maybe the problem is that we just don’t have enough symbols on our darned keyboards. The result is that we’re left fighting over the scraps that QWERTY gives us, e.g. the colon. My opinion is that a limited number of usable characters limits our thinking and our expressiveness. (emphasis mine)
In my recent quest to push forward awareness of capabilities, the notion of expressiveness seems to be at the crux of everything. If you don't have a conventional way to express something, it takes a lot of work to come up with something to get your point across.
I believe that rich source code is overdue. The idea first came to me via Chuck Moore's ColorForth, but I think it could be applied in a wider array of places. The ability to simply highlight a section and make it a comment without worrying about syntax would be cool, but I'm sure there are far more powerful uses that would quickly arise, such as the ability to do literate programming, freely mixing source and documentation and content.
The arguments against any new programming technique usually tend towards the fact that pretty much any language can already express any program. These arguments always miss the expressiveness that a new language brings to making it easier to solve a certain class of problem.
Friday, May 16, 2008
Originality
Thursday, May 15, 2008
Almost useful capabilities demo - 0.012
The main page at http://127.0.0.1:81 is now the user page, with the protected content. You have to have a capabilities token to edit the data.
The administration page is at http://127.0.0.1:81/admin, which allows you to create and revoke capabilities, and see the current "protected content".
It's all implemented in python, in a single file, just to make it easy to demo.
The slow road to implementation
http://warot.com/python/ contains my recent python programs. I have to name them with .txt on the end or the web server tries to run them (and fails).
So far I've managed to get up to webserver008.py, which manages to create random numbers and keep a list of them available. At the rate I'm going, I'll have something usable in a few months, which is better than never. 8)
Should you choose to actually download and run the thing... here's what it does.
In a DOS box (or your command line equivalent)
Welcome to Mike Warot's capability based security demo web server, version 0.008
You can access it at http://127.0.0.1:81
Use control-c to tell it to shut down, which may take up to 10 seconds
started httpserver...
If you then open http://127.0.0.1:81 in a web browser, you'll get a very informative message like this:
this is the default content, not served from a file
Here are the valid tokens:
Now.. for the completely undocumented and poorly written section of code... change the URL to http://127.0.0.81/token, and you'll get something like this:
0451a66530b72a980725745c39992239
Isn't that lovely? If you then go back to the home page at http://127.0.0.1:81 and refresh the page, now you'll see:
this is the default content, not served from a file
Here are the valid tokens:
0451a66530b72a980725745c39992239 [Revoke]
That's a list of all the tokens, with the ability to revoke one of them. That's pretty much the full extent of the power of this demo.
It's a list, with a undocumented, poorly designed and inconsistent UI... but it's a step in the right direction. Oh... and it's licensed with the GPL so you can fork the project. ;-)
I hope to get a reasonable list view with the ability to issue tokens without having to mung the URL in the next day. Code to actually give out capabilities to edit a resource should be next week.
It's slow going, isn't it?
--Mike--
Computer as suspicious package
I haven't actually had total control over the contents of a computer since I built a little box back in the 1980's that watched for a ring signal on a phone line, flipped the relay to pick up the line, used a 4 channel 8 bit A/D converter to sample 4 incoming voltages, then used a speech chip to speak the given voltages (in almost recognizable english) to the caller, twice, then hang up.
I wrote the code, programmed the 2764 EPROM, and it was totally under my control. I packed that piece of hardware... but since then... no way.
If you get a new PC from a good source, you can reasonably trust that the BIOS isn't going to be subversive. Once you load an OS, you've definitely had someone else doing your packing.
If it came loaded (or used)... there's really no way you can truly trust it, you just have to assume it's all going to be ok. Most of the time, it works out that way, or if it is a zombie on a botnet, you don't even know it, which is almost as good for most people.
It's a strange thought... but one I think might provoke some discussion.
Tuesday, May 13, 2008
Only Communists complain about twitter??
Twitter breaks, a lot... it's broken now, giving me time to write this. It's ok to complain about a broken service. Twitter is a good service, when it works, but it's too valuable to leave to the winds of chance. Thus... replacing twitter with something more reliable is a natural itch.
I guestimate that the aggregate flow through twitter is somewhere around 3kbytes/second when it's at full bore. It can be replaced with a set of machines, with normal code, and normal network hardware. There's no super hardware or non-obvious patentable code buried in it... anyone with enough programming skills, hardware and time could do it.
But... even hinting that we might do this sends Cliff into a 1950's McCarthy era rant about communism... it's just.... odd.
Being able to trap keywords and subscribe to them from the overall stream still only has to content with 3kbytes/second. Again... normal hardware, normal networks, just a bit of distributed software to make it all work.
Even more stuff to choose... ugh!
I'm like a newbie all over again... I've kept up a little bit on the buzzwords, etc... but haven't had to actually implement anything from scratch in more than 12 years. I figured surely in the meanwhile all of this stuff would be sorted out, and there would be a nice standard way to have programs talk to each other across the internet.
So now I know what all of those buzzwords like SOAP, XML-RPC, REST, WDSL and the rest mean... nobody has a nice simple way to do things...
I was hoping to do a nice simple demo of a RESTful capabilities system using Python as a simple standalone app that anyone could just put on their PC (or server). It turns out that there are several things in the way. Here are some of the things I've learned.
- Cryptographic random number routines aren't included in python. (Dean Landolt suggests punting the issue and getting on with it... and I agree for the demo)
- The library that would do it requires me to be able to re-compile python (using Visual Studio 2003)
- REST isn't... the common example of Flickr as a RESTful API isn't.
- WDSL is for people who like to write specification specifications, and don't write code.
- REST is the choice, except that web browsers don't actually PUT or DELETE, and a lot of people use GET for things with side-effects.
- There are a lot of python web toolkits out there, including CherryPy, TurboGears, Web.py, Django, and others.
In spite of all that, here are my design choices to date:
Programming language: Python, because it's cross platform, a known entity, and quite powerful, despite the immutable strings, and comes with a web server library.
Database: None - it's a demo
Random Salt: the built in non-secure RNG from python
Protocol: REST-ish... GET for reading, idempotent operations only, POST for everything else. Rest because there should only be one URL per object, regardless of the compromise about PUT/Delete.
The demo will be of the ability to edit a string. You'll be able to see the string with a straight web page. You'll be able to request a token to edit the string, you'll be able to write the string (provided you have the token) and you'll be able to revoke the token.
I'm hoping that's simple enough for me to get done on a few train trips to/from work.
Monday, May 12, 2008
Random numbers are hard... whoda thunk it?
So, eventually I'll find what I want (or be forced to port it myself)... and then I can get back to the examples... which will generate a token consisting of the object, the capability, and a random number to serve as salt to keep from having it forged.
Wish me luck.
Saturday, May 10, 2008
Twitter - Capabilites mashup
#1. - Get rid of user accounts on twitter... just hand out the capability to post, which would be different each time it's issued, and individually revoke able. I'd hand them out in an Email, to limit the user base a bit and cut down on spam. You could always store the email address somewhere in a table along with the capability to know who it is if necessary.
#2. - Allow each user to then hand out tokens that would allow a direct message, which they could proxy and/or revoke themselves. This would make it possible for an end user to block someone from making direct messages, without the need for it to happen in the central code. The proxy that does this could be a separate service, and doesn't play a part in the security of the central capability provider code.
#3. - Allow each user to hand out tokens that would allow following them, which like above, they could proxy and revoke themselves. This turns the distributed twitter into an effectively private email system without too much work.
#4. - There's really not much difference between a tweet and a blog post, other than length. There's not much different between a private posting and and email... you could cover all of them this way.
Ok... it's 10:30 and I'm sleep deprived, so this might not be as coherent as it seems at the time... though I hope it is.
Capabilities offer a huge amount of flexibility when doing system design. They make it possible to break apart the logic of a complex application without having to worry about the combinatorial explosion that results from the conventional idea of having every piece of code enforcing a ton of rules.
What do you all think?
--Mike--





